The configuration of the cisco anyconnect vpn is rather simple, I am using local user account to login to the vpn, however my client experienced a problem in authentication.
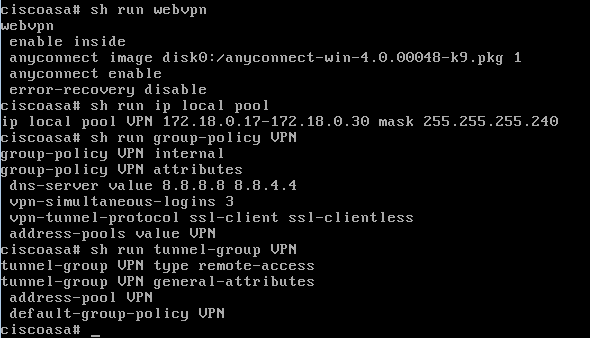
See the vpn configuration:
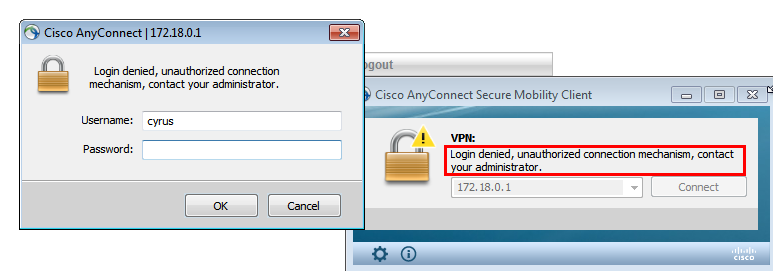
This is a very straight forward configuration, however I could not use anyconnect client to login:
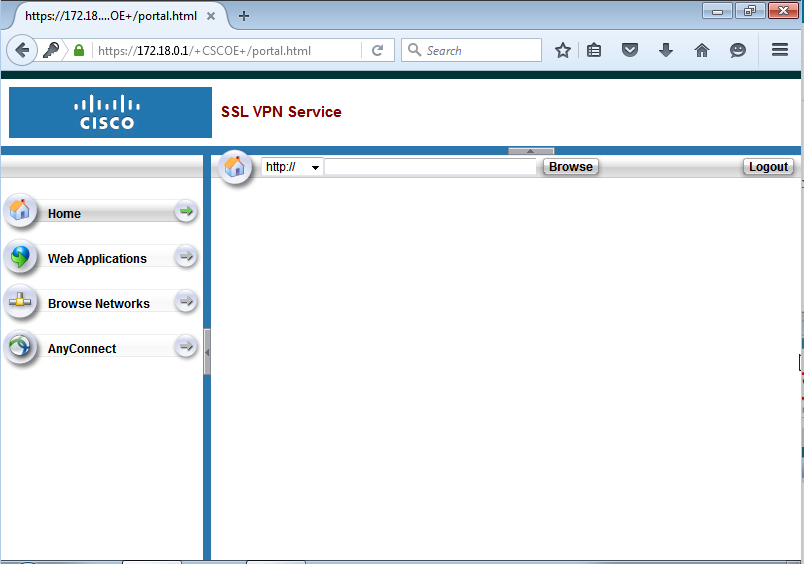
I can however login to webvpn (clientless)
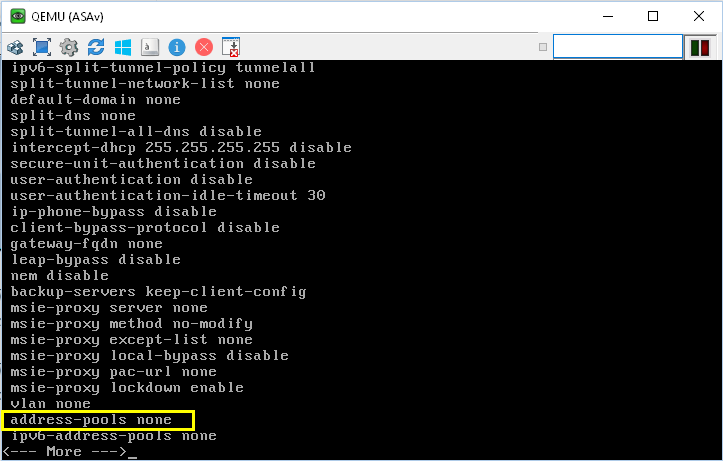
So… what is the problem? Cisco ASA comes with “built in” default group policy known as “DfltGrpPolicy”. You cannot see these default group-policy with just “show run” you need to do “show run all group-policy DfltGrpPolicy” to actually see the default settings.
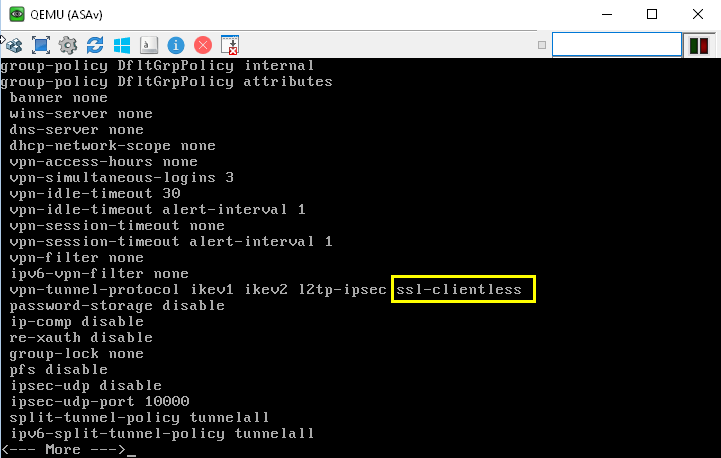
So there is no ssl-client in vpn-tunnel-protocol?! Screw you Cisco! If you want to put default setting you jolly well do it fully! Why don’t you include ssl-client in the vpn-tunnel-protocol?
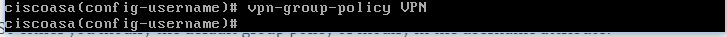
So in here you either put in ssl-client in the DfltGrpPolicy or in local username attribute you specify your own vpn-tunnel-protocol per local username.
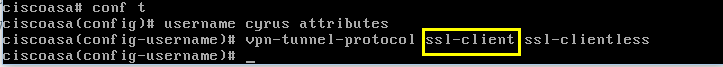
The error message “Login denied, unauthorized connection mechanism, contact your administrator” usually means the ssl-client is not specified in vpn-tunnel-protocol.
So how does Cisco respond to this kind of error in its troubleshooting guide?
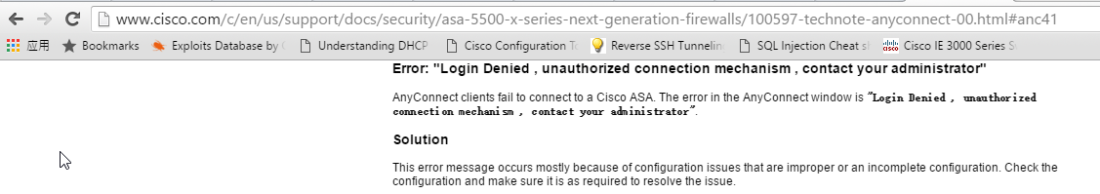
Screw you twice Cisco! Which part of the configuration is not complete?
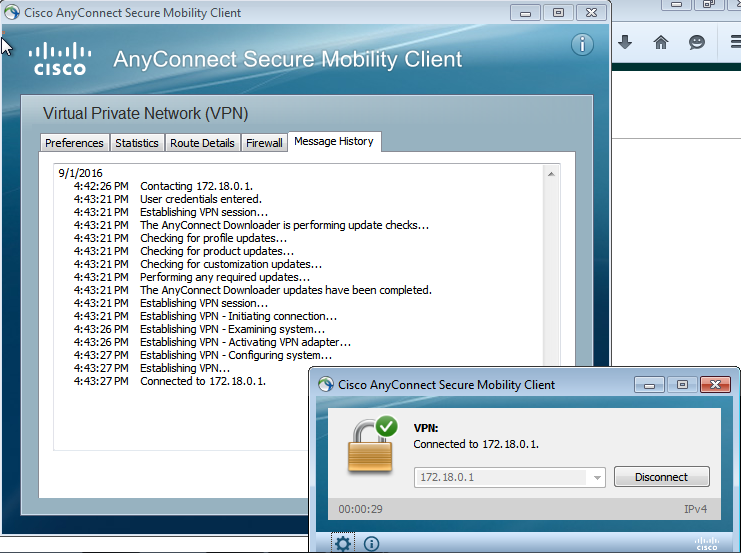
So after I have included ssl-client in vpn-tunnel-protocol can I connect?
NO….! I cannot connect, for goodness sake this is only local username….
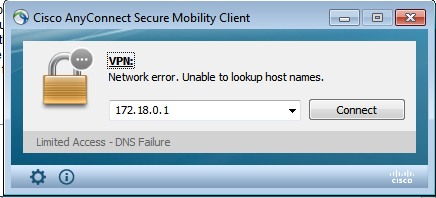
What?! Network error? Screw you triple Cisco! From the message log in Cisco Anyconnect client connection was rejected because there was no address pool assigned!
Why? Because of the bloody “invisible” and made visible if you use “show run all group-policy DfltGrpPolicy” command!
So either you modify the default group policy or modify in the username attribute:
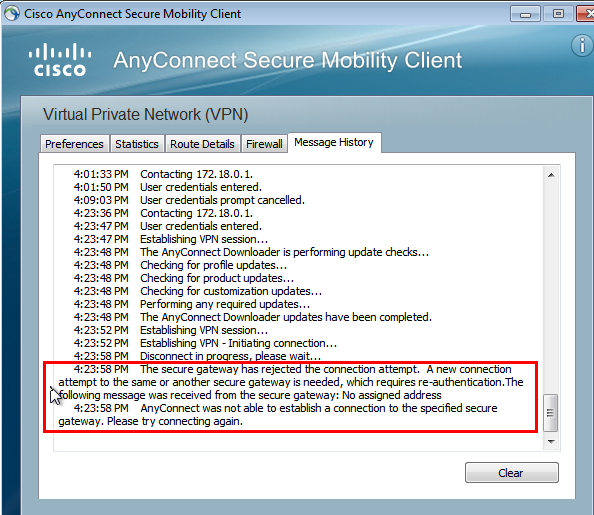
So finally it gets connected, happy ending?
NO! Look at this shit:
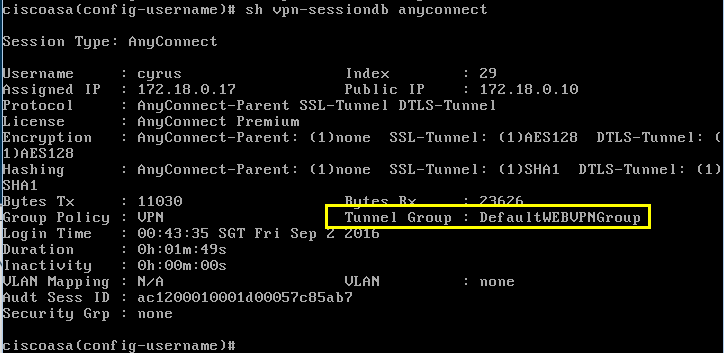
I do not want Cisco’s defaults! I want mine! So either I group-lock the tunnel-group in my group-policy or I group-lock in username attributes.


The early carriers operated by the Royal Navy were equipped with a combination fighter-dive bomber aircraft called the Skua as well as biplanes armed with bombs or torpedoes such as the famous Swordfish. Gambling or any reference to gambling (Poker, Roulette, Blackjack, Betting etc). When you’re in a vehicle you are usually defenseless.
We absolutely love your blog and find many of your post’s to be exactly what I’m looking for. Does one offer guest writers to write content in your case? I wouldn’t mind composing a post or elaborating on a few of the subjects you write regarding here. Again, awesome site!
Or you could have just used the Wizard
I’m still learning from you, while I’m trying to reach my goals. I definitely enjoy reading everything that is written on your site.Keep the information coming. I liked it!